As legal showdowns go, Apple v. FBI came in like a lion and left like a lamb. In February, the Federal Bureau of Investigations (FBI) won a federal court order to compel Apple to build a new operating system that would allow agents to hack into the iPhone 5 used by the San Bernardino mass shooter. When Apple refused to comply, some commentators claimed it was the biggest showdown over surveillance in the last decade.
While this legal showdown was still grabbing headlines, National Security Agency (NSA) whistleblower and cyber security expert Edward Snowden called Apple’s refusal to cooperate important on principle. But he correctly asserted the FBI’s claim it was unable to access the iPhone due to Apple’s encryption was “bullshit.” On March 28, the FBI dropped the legal action after an unnamed contractor helped the Bureau bypass the encryption.
Nonetheless, encryption, is still a key privacy tool. As Snowden himself put it during an online Q & A hosted by The Guardian in 2013: “Encryption works. Properly implemented strong crypto systems are one of the few things that you can rely on [to protect your privacy].”
This is a broad statement, however, because there are different types of encryption for different types of functions. The most secure forms are made with open source software, which make it possible for technicians to see how the programs work and also makes them free for individuals to download and use. Although there are free tools that can secure information from even the most well resourced attackers, like the NSA, few organizations use encryption, let alone worry much about what types of encryption to use.
Case in point: Mossack Fonseca, the self-described “legal services firm” that was the source of the Panama Papers. A whistleblower concerned with the unethical and illegal nature of the company’s business provided 2.6 terabytes of data from its internal network to International Consortium of Investigative Journalists, which began publishing the material through various news outlets in April.
The term “Legal services firm” in Mossack Fonseca’s case is a nice way of saying “money laundry.” As the Panama Papers reveal the firm set up shell companies and provided tax havens to the globe’s wealthiest individuals. When the Panama Papers hit front pages worldwide, the company’s offices were raided by the police forces of four governments.
Mossack Fonseca’s behavior was not simply unethical and illegal, it was also stupid. As its own leaked internal emails show, the firm didn’t use modern, end-to end open source encryption tools; didn’t effectively educate its staff about what it was doing with digital security; and consistently undermined its security by creating anonymous and unlogged access points to its network. These types of practices make it easy for hackers, governments, or whistleblowers, for that matter, to access information systems that lack end-to-end, open source encryption.
Unfortunately, US government policy has made open source, end-to-end encryption important even for everyday people who are not engaged in nefarious activities. Mass surveillance is current government practice and it has made it necessary to defend our privacy in what many observers have begun referring to as the Golden Age of Surveillance.
Governments globally are working to ensure they can have access to all digital information all the time. Domestic law enforcement groups like the FBI have access to more and more information from massive government databases collected directly from the servers of all the major email providers. Here is how it works: the NSA collects information on Americans on a massive scale under the Foreign Intelligence Surveillance Act and Executive Order 12333, the FBI receives access to this data collected by the NSA through a partnership with the Drug Enforcement Administration’s Special Operations Division, which gives them information from all major US service providers — Google, Apple, Yahoo, Facebook. This enables domestic law enforcement to utilize the NSA’s Bluffdale Utah data facility, which has the capacity to hold 1000 times more data than the entire internet, a yottabyte of data.
In a 2015 report, United Nation’s Special Rapporteur on Freedom of Expression, David Kaye, argued that due to this type of widespread, warrantless surveillance of internet communications, anonymity and encryption must now be considered human rights. Kaye cites Article 19 of the International Covenant on Civil and Political Rights, ratified by the US in 1993, which affirms the universal “freedom to seek, receive and impart information and ideas of all kinds.”
Those of us wanting to uphold our rights should use open source, end-to-end encryption and demand the same of lawyers, businesses and others handling our personal data.
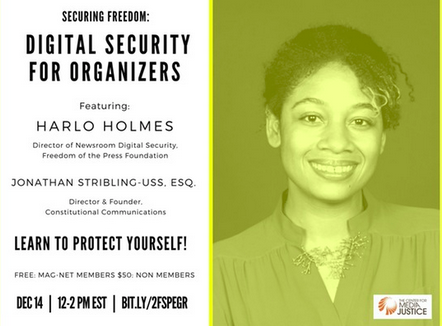
Jonathan Stribling-Uss is an attorney and Director of Constitutional Communications (concomms.org), a not-for-profit organization that trains lawyers, journalists and civil society leaders in maintaining secure communications.
6 Tools to Protect Your Privacy
1) Signal by Open whisper systems (in App Stores)
Signal is the easiest and most secure encrypted text and calling program, with more than one million users. The app is free and takes 3-5 minutes to get started. It can now be used with both your phone and computer.
2) Jitsi (Jitsi.org)
A free service, requiring no account, that allows for multiparty, end-to-end encrypted video calls and chats. For more usability you can install a download, but it is not necessary to get started calling friends around the globe.
3) Tor (www.torproject.org)
A free browser that uses encryption and a random series of open routing computers to separate your actions online from your IP (internet protocol) address, providing anonymity.
4) Make a longer passphrase with memorable words
With robust symmetric encryption, when you lose your password, you lose your data. This means that you have to create passphrases, not just words, that are easy for humans to remember but hard for machines to guess. The simplest way to do this is to use at least four random words, and a number or given name. For example; “correcthorsebatterystaplenatturner”.
5) PGP/GPG (www.gnupg.org)
A free, open source, end-to-end encryption system that has been used and tested for over 25 years. It is designed to supplement your current email address, so you don’t need a new email, you can just add this asymmetric encryption system over the top of your current provider.
6) Tails OS (tails.boum.org)
A free, open source operating system that can be run on most computer hardware and secures your traffic and data on an encrypted USB. It is based on one of the most used operating systems, Debian, and it is packaged with a full set of office and encryption tools.
— Jonathan Stribling-Uss